 Dynamics: The Geometry of Behavior, Ralph H. Abraham and Christopher D. Shaw (1992)
Dynamics: The Geometry of Behavior, Ralph H. Abraham and Christopher D. Shaw (1992)
From Stateless Money to Crypto States
The 2008 financial crisis incited a new era of institutional distrust. The public was forced to confront the unthinkable: that the monetary system itself was no longer working in their interest. The Occupy movement was one expression of public unrest, while others turned to Bitcoin and the promise of an incorruptible money powered by self-executing software as an alternative to fiat institutions.
However, where we once talked about separating money from state, now we hear of crypto states and constitutions. Political rhetoric in crypto has turned from state avoidance to state mimicry, with democratic voting models and public goods as primary concerns. Underpinning this slippage is a new ideological refrain: that crypto is the next “leviathan,” comparable to the state in its ability to instantiate immutable rights. According to some, blockchains will replace the state’s monopoly on violence with a credibly neutral decentralized cryptographic infrastructure, allowing for the creation of independent property rights and “network states.”
While we celebrate experiments in institutional formation through software, in the enthusiasm to rehearse 18th century radical politics, these endeavors have forgotten the central feature of the state: the regulatory power of law. When Silicon Valley Bank goes under, the state can act unilaterally to guarantee its deposits. Crypto has no such function. When a protocol gets hacked, everyone loses their money and only an overwhelming majority can produce a fork to restore user funds.
Censorship-resistant immutability is crypto’s greatest achievement as well as its greatest weakness. By resisting the all-encompassing reach of the law, it creates the conditions in crypto for a new kind of realpolitik, a space where power operates by different rules. However, in removing the law, crypto protocols are left with a three-body problem. Social norms, markets, and code each have their own regulatory logic, often finding themselves in conflict. In this novel game board, protocol designers’ intentions can be undermined, leading to undesirable institutional behaviors, moral dilemmas, and contradictory governance policies.
Interventions that seek to bolster the normative regulatory dimension show promise for addressing these limitations, but they are often squashed by the primacy of hard-coded market incentives. Maybe the answer to strengthening normative self-regulation is to be found in already-existing cultural contexts.
The Regulatory State
Software may be eating the world, but it’s a world already consumed by law. Through law, humans become legal persons with rights, “nature” is defined and protected, and order is sought across land and sea. Pervasive and plastic, law is the essential institutional technology of the modern nation state. While the nature of law is still an object of scholarly debate, its chief feature is clearly the regulation of behavior. The law imposes standards of conduct that uphold communal values and protect liberties. Likewise, the law enforces sanctions that deter or punish acts of harm.
The law of the state is not the only force that regulates the res publica. In his landmark 1998 article, Lawrence Lessig discussed how a total of four forces—law, markets, social norms, and the architecture of the built environment—govern daily life. Norms dictate what is socially admissible; markets regulate economic exchange through the mechanisms of price; while architecture acts to delimit space and orient flows of people and information. Finally, the law regulates behavior through the instruments of institutional privilege and enforcement. Together these forces determine the space of the possible, given the material, social, and economic circumstances. “We the people” are just “pathetic dots” subject to these four regulatory powers.
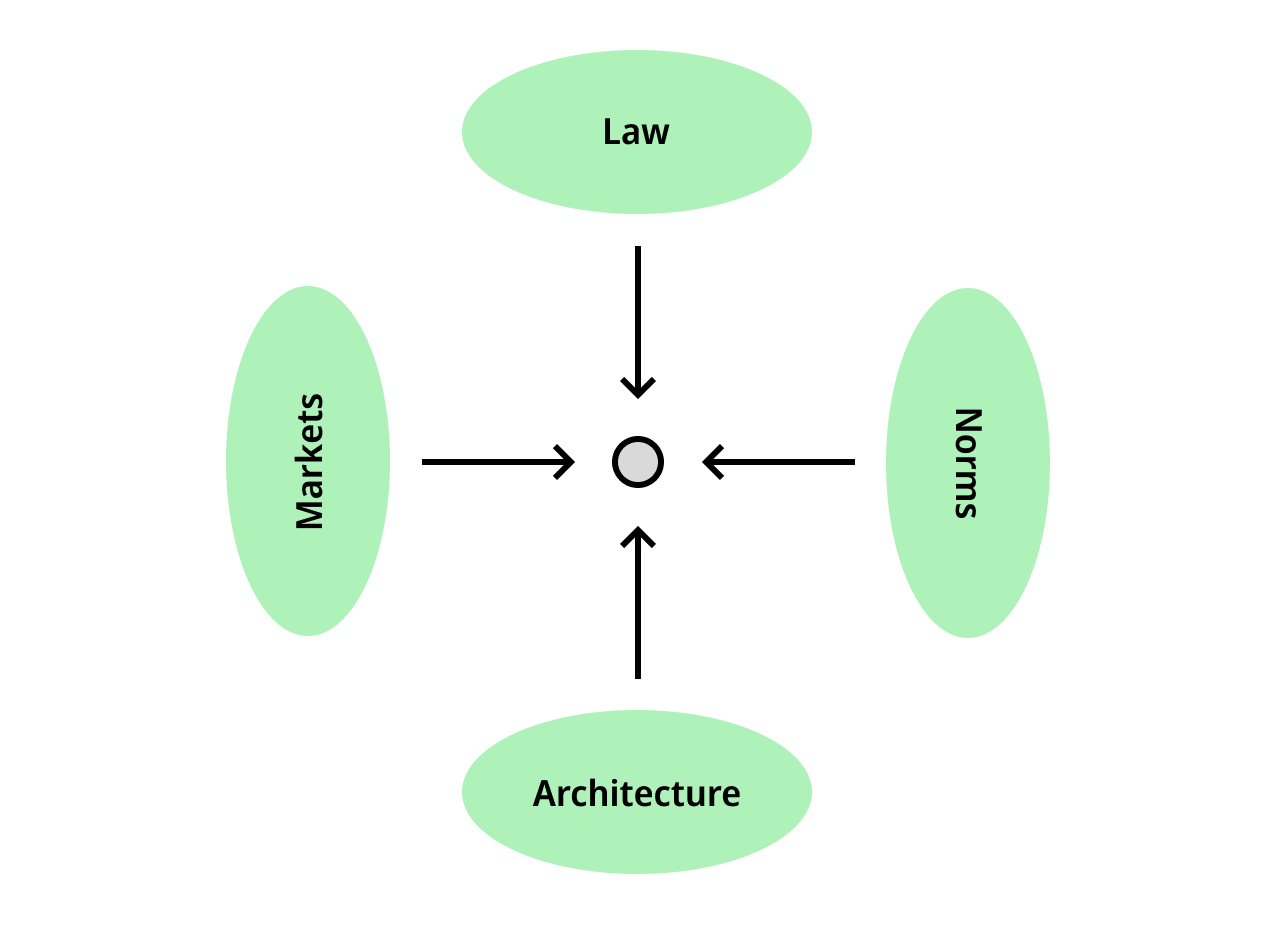 The four modalities of regulation that constrain behavior for the “pathetic dot”. Adapted from Lessig 1998.
The four modalities of regulation that constrain behavior for the “pathetic dot”. Adapted from Lessig 1998.
Of the four forces at play, law occupies the supreme position within the state. Lessig strove to show how law bends the other regulatory forces to its will, regulating through them. For instance, the law regulates via markets when Japan institutes high taxes on foreign rice imports, ensuring Japanese consumers eat domestically-grown rice. Having lived through a global pandemic, we are all familiar with the public health campaigns that created social standards around mask-wearing and vaccination: the law’s regulation via norms. And insofar as technologies constitute a part of our digital “built environment,” the law attempts to regulate them as well.
However the power to regulate through other forces often becomes the power to regulate all. Take the Digital Millennial Copyright Act (DMCA) for example, which made it illegal to access content locked by Digital Rights Management, reinforcing the grey market for digital piracy. While the DMCA was a controversial and ultimately failed policy, it reveals the law’s expansionary tendency. The law is inclined to grow to the size of its container, regulating new technologies and social phenomena as they arise, even if lawmakers have not fully understood their significance.
The architects of social contract theory—among them Grotius, Locke, and Rousseau—could not have anticipated a modern regime in which the law seeps into all corners of life. But the law’s predominance is an inevitability. The law does not merely punish and constrain; it may also empower and provide assurance. Through the law, minority rights can be protected and conflicts between parties can be adjudicated. And although the moral arc of the law does not always bend toward justice, the law nonetheless provides a base layer of perceived neutrality, including clear pathways for citizens to update the rules of the game. If the state, as Max Weber claimed, is a human community that successfully maintains a monopoly on the legitimate use of violence, the rule of law is the tool that the state uses to achieve that end. Lessig himself is wary of his own ideas’ implications:
The regulation of this school is totalizing. It is the effort to make culture serve power, a “colonization of the lifeworld.” Every space is subject to a wide range of control; the potential to control every space is the aim.
But today the state’s sovereignty is being challenged. While this process started long before crypto, blockchains escalate this struggle to an entirely new level. Indeed, the regulatory complex composed of state, federal reserve, and “too-big-to-fail” banks is precisely what cryptocurrencies undermine. But in order to understand just how blockchains introduce a new type of regulatory regime, we need to turn to their fundamental novelty: censorship resistance.
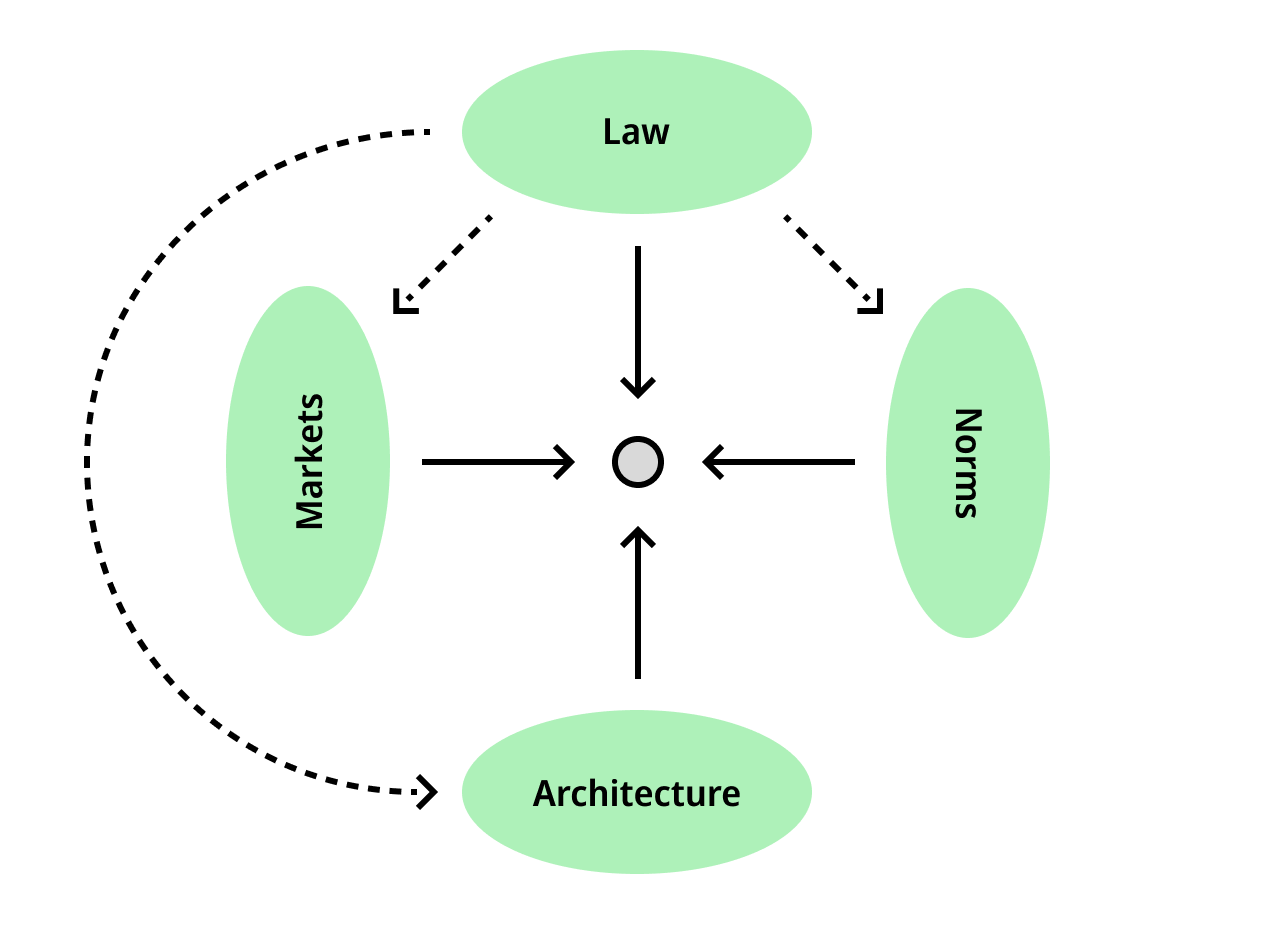 The law acts on other forces, regulating through them.
The law acts on other forces, regulating through them.
Censorship Resistance == Law-Resistance
While the state is still the only social body to claim the exclusive legitimacy of its regulatory power, a host of competing interests, technologies, and economies of scale encroach on the supposed sovereignty of law. International commerce is increasingly mediated through private dispute resolution centers instead of through international agreements. Meanwhile, the alliance between global finance and software challenges state regulation of markets altogether; when Elizabeth Truss' plan to cut $50bn in taxes caused the UK bond market to implode, she was forced to resign from the prime ministership after only 44 days. But if international finance has proliferated new regulatory bodies, its twin in power and influence is the internet.
Since its inception, the “architecture” of the world wide web has made the landscape of contemporary governance yet more complex. More than a medium for communication, the internet is a transmission layer for new regulatory powers. Networked computation enables the creation and expansion of new norms, markets, and architectures, implemented at multiple levels of abstraction. Social media platforms, for instance, have their own semi-automated free speech policies ignorant of the state’s, while the content of social media includes distinct normative regimes, including e-ideologies and morally coded diets. Remote work introduces new affordances for citizenship arbitrage, while internet-disseminated subcultures create imagined communities as strong as any national identity. The law of the state, even in regions like China where law is tightly coupled with the internet, is usually left playing catch-up.
 Estonia e-citizenship card, which can be obtained via online application.
Estonia e-citizenship card, which can be obtained via online application.
15 years ago, a new contender entered the arena: cryptocurrencies. In some ways, cryptocurrency protocols recapitulate the regulatory innovations of the internet. But they also generalize the censorship-resistant properties of previous networked technologies like BitTorrent and PGP. Crypto protocols cannot be tampered with by middlemen or higher authorities. And while the long arm of the law can force Facebook to open our DMs for inspection, or seize a pirated e-book host, as long as there are miners out there running nodes, Bitcoin and Ethereum assets are accessible and inalienable; computed state is irreversible. In other words, these protocols have no regard for the law. Cryptocurrency protocols are monetary and contractual media without the need or validation of state authorities. They have created a new sort of regulatory institution, one which is not only resistant to censorship but resistant to law itself.
This is not to say that crypto protocols are just technologies for criminal, lawless activities. Law-resistance is also what fuels the positive vision of improving legacy organizations and confronting social coordination problems by designing ground-up credibly neutral institutions—money systems, banks, and commons. By “law-resistant,” we therefore mean to say that Bitcoin and subsequent crypto protocols are resistant to the regulatory base framework that, in Lessig’s model, operates as a pervasive totality. As blockchains resist the state’s law, they also institute a regulatory regime of their own. And without law able to intervene, the remaining three forces are free to regulate the institutional ecosystem of crypto protocols without a unifying arbiter. Let’s look some of the novel institutional dynamics that protocols make possible.
Three-Body Regulatory Problems
The unruly interaction between the software architecture, markets, and norms in the absence of law is what we call crypto’s three-body regulatory problem.
➊ Cryptocurrency protocols are made of a technically encoded architecture with a few notable aspects. Cryptocurrency protocols are open source and permissionless, meaning that they are accessible to most anyone in the world with an internet connection. They deterministically process computation, and introduce significant friction to reversing the protocol’s highly replicated state. In terms of interaction surfaces, protocol architectures are tightly constrained: they provide only limited, specially defined affordances for interaction (e.g. Application Binary Interfaces). This is one of the keys to understanding the regulatory apparatus of the protocol: participating in crypto’s regulatory regime means, ultimately, interacting with smart contracts or blockchain code.
➋ Crypto protocols are driven by global, 24/7 markets. When users interact with cryptocurrencies, they do so through the deterministic logic of hard-coded market structures—token supplies, reward functions, bonding curves, lending and exchange rates, automated market makers, etc.—which collectively compose a second regulatory regime. The requirement that blockchain states are computed by sending transactions means that certain markets and architectures, such as Ethereum, are tightly coupled. It is for this reason that many of crypto’s markets still elude legal oversight, as the law cannot reverse a processed transaction. The blending of markets and programmable code also explains the focus on incentive mechanisms as the holy grail of protocol design and the favored tool for "stakeholder alignment."
➌ And finally we have a social-normative layer, held together by a multifaceted web of on- and off-chain communication channels, what we commonly refer to as “the space.” The crypto community has been populated by a wide array of subcultures: cypherpunks, yolo traders, platform cooperativists, activists of all forms, e-girls, born-again Christians, post-internet artists, neo-rationalists, effective altruists, and accelerationists of various flavors and speeds. Each group has brought its own norms, and many have designed protocol-based projects to suit their politics. While each microculture has its own specific traits, most of them share one thing: a persistent ethos of self-managerialism and anti-institutionalism. This norm seems to be part of what attracts different groups to crypto in the first place, even turning would-be-bankers into P2P cash advocates.
Because the regulatory forces affect each other, different combinations have effects on the overriding incentives and long-term social development of a given system. Lessig notes that regulatory forces can sometimes “substitute” for one another: for instance, using speed bumps and traffic circles can achieve an effect that might otherwise be accomplished by the costly strategy of employing a large police force to issue more speeding tickets. But the capacity for substitution is greatly weakened without the law’s unifying regulatory power.
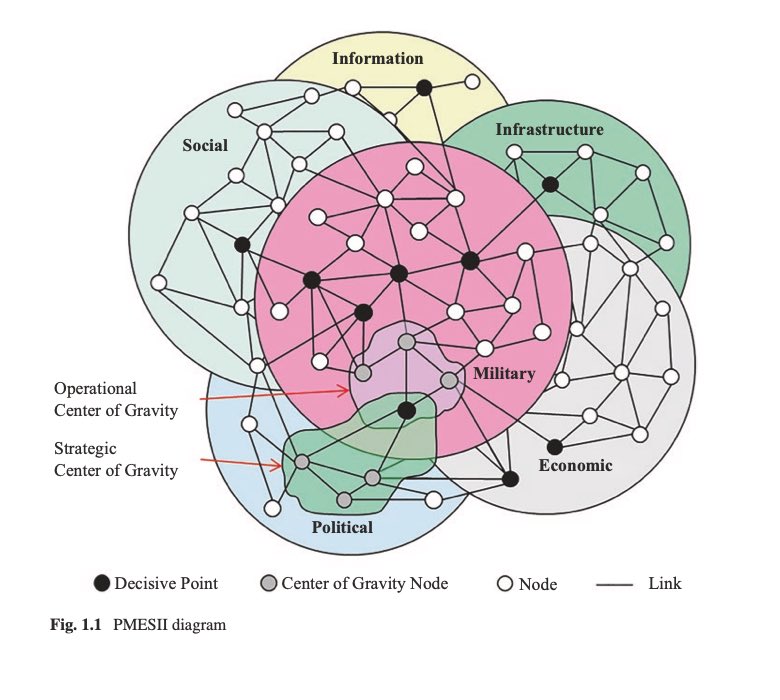 Source: Defense Charts
Source: Defense Charts
Crypto has no such integrative force. No meta-normative logic to convert collective notions of justice into a regulatory strategy that can be implemented across all domains. In its absence, the unstable interactions of norms, markets, and architecture have spawned new and often surprising institutional behaviors. Let’s take a look at how this three-body problem has played out in several protocol contexts.
Curve is a DeFi protocol which distributes a fixed set of rewards at a regular cadence. Yield is allocated based on a time-locked staking calculation: a user’s tokens multiplied by the lock duration determines their vote escrow (ve) power over the amount of incentives provided to a given pool.
Relatedly, the Convex protocol was built to “boost” rewards for CRV stakers and Curve LPs, effectively creating a secondary market for votes. With Convex, market participants in need of liquidity can pay users who have locked funds with Curve to direct their liquidity voting power. As a result, the community has adopted the language of black markets and bribery to describe this system, which does in fact describe the core institutional logic of the Curve/Convex protocols, setting accurate expectations for how to engage with them.
Curve demonstrates what is novel about protocols as institutional frameworks. Without human management, the coupling of programmatic incentives and free markets introduces an institutional behavior—bribery—that is expressly disallowed in legal settings. As a result, social norms are reoriented to validate and reproduce said pattern. In other words, norms become indistinguishable from market incentives. The acceptance and normalization of these incentives is visible in the fact that no attempts have been made to constrain or change this dynamic; it is simply allowed to work. We don’t bring up this example to endorse bribery or to validate veToken mechanics, but to point out that the core logic of the protocol and its popular understanding are in fact aligned.
While there are many more examples of peculiar and sometimes questionable institutional logics in crypto, this case illustrates both the affordances and limits of the protocol’s regulatory influence. With the alignment of all three forces, even bribery can be seen as an acceptable outcome. But there is not always harmony among the regulatory powers. In the battle over NFT royalties, for instance, all three forces conflict.
Many popular ERC721 NFT implementations make use of hard-coded royalties that pay the original creator a small fee each time the NFT is resold. This is a market structure designed to satisfy a specific normative claim: creators should derive returns from the value they generate. Some of the largest NFT marketplaces and protocols respect these royalties, even giving users options to add additional tips to the original creator. But crypto’s open source, permissionless architecture makes it possible to “wrap” these NFTs in other smart contracts, which can be sold and then unwrapped, avoiding the fee.
When the NFT marketplaces Sudoswap and Blur launched, their designers chose to implement these workarounds, ignoring existing norms and undercutting other venues. This competitive move forced OpenSea, the largest NFT marketplace, to follow suit by making royalty payments optional. This story ends unhappily, with crypto-enthusiastic artists feeling betrayed by the medium and by popular marketplaces. A market structure could be designed in alignment with norms, but it could not be enforced.
Protocol designers often assume that markets, code, and norms will harmonize according to their own plans. But this is frequently not the case. Unlike the generally-aligned legislation of a given jurisdiction, the space of protocols is anarchic and disorderly. Protocols with different norms compete for resources and attention, using incentives to attack one another, or imploding in the occasional hack or rugpull. In the rise and fall of NFT royalties, smart contracts enforced fee payment only briefly; and in the end were no match for the contingencies introduced by a permissionless meta game. All contracts are incomplete, but smart contracts are especially so. Here, one aspect of technical infrastructure proved dominant over the other.
Without the law, attempts to use other state-inspired instruments, such as constitutions, role appointments, and subjective rules often fall flat. Let’s look at one more case where smart contracts overruled other institutional design patterns.
ENS is one protocol that has developed state-like features, such as the ENS DAO constitution, “democratic” governance process, and public goods emphasis. Each of these instruments suggest a larger promise to stakeholders: that the norms and values of the ENS community are represented by the protocol’s institutional behavior.
These expectations were challenged when a hateful 2016 tweet by ENS co-founder Brantly Millegan resurfaced after 5 years, attracting the ire of the crypto community. Millegan became subject of a de facto cancellation campaign which culminated in a vote by ENS tokenholders to remove him from his position at the ENS Foundation, a legally instantiated Cayman Islands entity. Leaving aside whether the action was justified or not, what is interesting to consider is the obvious misalignment between the tacit normative expectations of ENS tokenholders and what the protocol mechanisms allowed.
A controversial feature of the vote to remove Millegan as foundation director was that it failed in part due to Brantly himself voting against the proposal. Without Millegan’s vote as the largest delegate, the majority of votes would have triggered his ouster. Although many in the ENS community expected Millegan to abstain, any legally binding social rules, such as bylaws, must necessarily sit outside of the protocol. The ENS “constitution” that ENS airdrop participants had to sign to claim their tokens did not contemplate such a case, nor were such contingencies designed into the voting system.
Just because protocols are able to regulate some behavior does not mean that they have the full regulatory capacity of the state. Linguistic rules such as bylaws, constitutions, and codes of conduct are extremely weak without law’s retroactive enforcement mechanisms. Legal bodies use these texts to infer the intent of parties involved in a contract, but protocols have no such ability.
Protocols include a variety of enshrined architectural features to facilitate coordination. Likewise, the creation of digital property rights with programmable controls has enabled an array of permissionless markets. However, as a protocol transitions to greater community-operation and takes on more complex administrative functions, the social challenges also become more demanding. In such cases contention cannot be addressed solely through programmed financial incentives but requires an added layer of discretionary logic tied to the values that a community upholds. In short, when conflicts among the three forces inevitably arise, they cannot be resolved through traditional, legal means.
Regression to the Code
We’ve demonstrated how institutions regulate behavior through the arrangement of effective forces, and how the behavioral dynamics innate to crypto are the result of regulatory instability in the absence of law. While law may not be entirely self-coherent, it does at least provide a single jurisdictional surface through which all other regulatory forces may be altered. In contrast to the state’s overarching regulatory system, life within the jumbled patchwork of crypto protocols is a far more untethered and and risk-prone condition for inhabitants. This hasn’t stopped brave people from migrating their assets to the digital frontier. But how do crypto-citizens reckon with the frequently contradictory outcomes of the 3-body regime? A protocol’s ability to credibly enforce discretionary principles is substantially less developed than the state.
Readers will observe that in the three cases explored above—Curve, NFT Royalties, and ENS—institutional behavior tends toward “regression to the code.” By this we mean that whatever role norms play in a protocol ecosystem, the ultimate determinant of institutional and user behavior is the encoded architecture and market incentives. With Curve, we saw “greedy” behavior was a valid social norm enabled by vote-buying mechanisms. With NFT royalties, we saw artist-supporting residuals collapse in a price war. And with ENS, the in-built coin voting system overruled the community’s normative stance on Brantly Millegan’s removal and abstention. When normative behavior is unenforceable, it tends to regress to behaviors afforded by the other regulatory forces. New social norms that correspond to the extant architecture then prevail.
Some view this regression phenomenon as the foundational policy of the crypto space: “whatever is permitted by the protocol’s code and market structure is legitimate.” This viewpoint, while rarely expressed in such direct terms, is remarkably common among crypto users. It is certainly present in the Curve case. It is also what is voiced when one defends the rights of hackers to exploit poorly designed protocols. As the hacker of Mango Markets infamously stated, his team merely “operated a highly profitable trading strategy.”
However, regression to the code doesn’t always produce legitimate outcomes, so it can’t be true all the time. In the cases explored earlier, the legitimacy of protocol adjudication is precisely what is in question. It is not clear, for example, that the inability to protect artist royalties is a good outcome. Many viewed it instead as an architectural shortcoming, taken advantage of by unscrupulous traders who skirted designers’ good intentions.
Regression to the code erodes social norms, and this consequence accounts in large part for what repulses people from crypto. Even as protocols fulfill important social functions like affordable remittances and escape from inflationary regimes, “the space” appears to outsiders as greedy and riddled with scams. It is for this reason that crypto seems to stand apart from all prior human institutions. More than just “lawless,” it comes off as a “normless” zone where morality is suspended, even if the prevailing intention is to support the resiliency of all manner of social organizations.
 The Hex token, an early example of the new discipline of ponzinomics.
The Hex token, an early example of the new discipline of ponzinomics.
So the pervasive belief that anything permitted by the protocol is unquestionably legitimate is obviously harmful. But the true culprit behind this poisonous idea is the principle of credible neutrality. According to the doctrine of credible neutrality, the unbiased nature of a protocol implies the validity of all actions that take place under its purview. This includes not just contentious governance outcomes, but social violations such as hacks or scams that are technically permissible and yet tolerated in the name of neutrality and permissionless access.
This is not to say censorship resistance should not be upheld as a fundamental technical property. However, there needs to be room somewhere for facilities that prevent user harm. Invoking credible neutrality should not have the primary effect of degrading accountability and putting users at risk. To make an analogy, one can endorse net neutrality, that is, non-discriminatory packet transport, without going so far as to foist dark UX patterns onto users. The question then is where and how is this regulatory force to be applied? Any such instruments of consumer protection must ultimately be self-regulated by protocol actors (interfaces, relayers, solvers) that remain answerable to users.
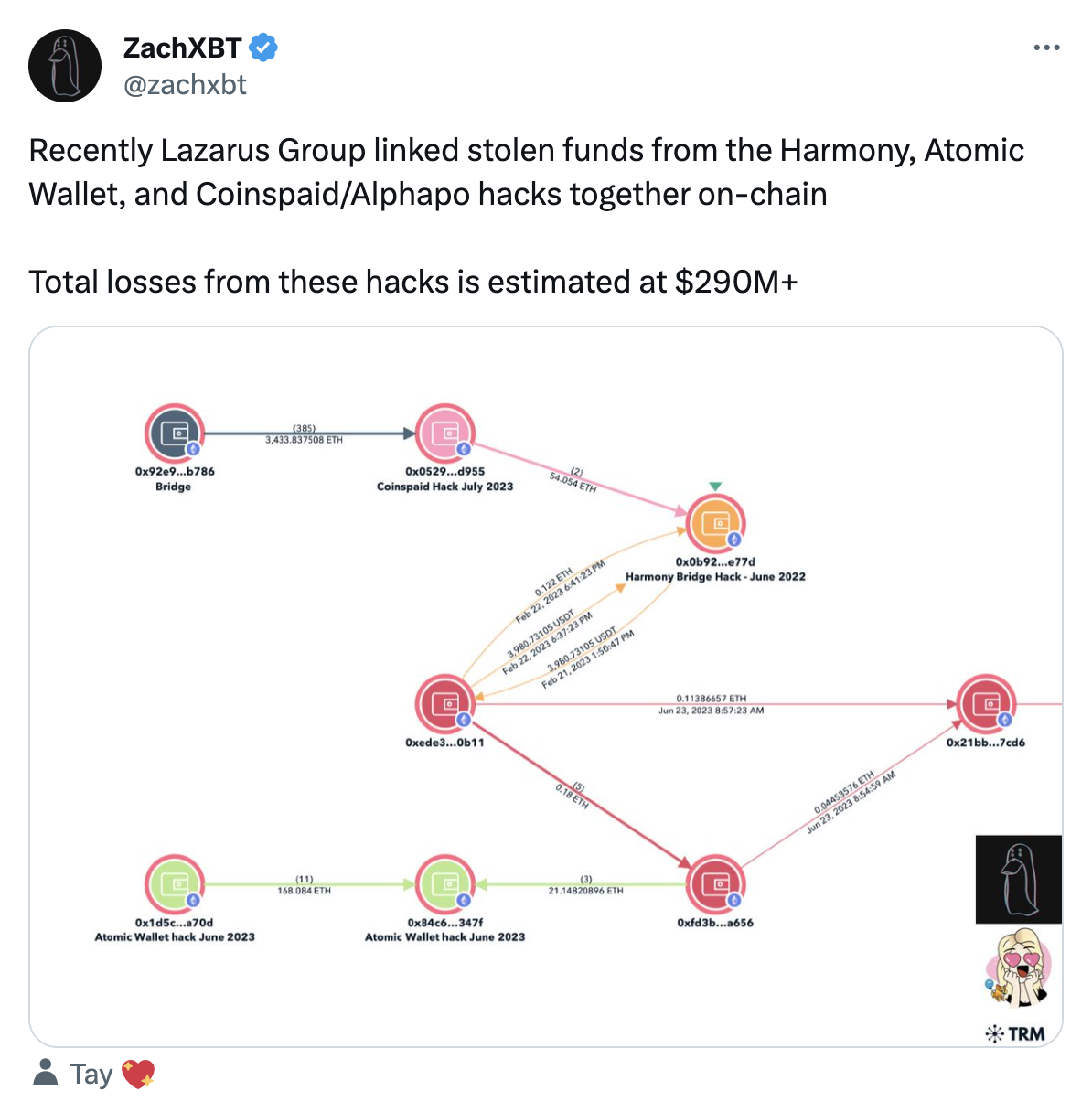
Even within the stifling discourse of credible neutrality, there is a desire among some protocol designers and users to make norms a larger part of crypto’s self-regulatory function. In response to the paucity of effective normative regulation, a small cadre of self-regulating parties have stepped up to promote different forms of social welfare. Two institutions in particular have managed to get social buy-in by activating cross-cutting values shared by many in the Ethereum ecosystem: the public goods project Protocol Guild and the vigilante investigator ZachXBT.
Users who notify others about scammers and front-end interfaces that de-list scamcoins are acting on moral grounds to protect others. ZachXBT is one prominent on-chain researcher who documents and exposes scammers to whom the crypto community has previously turned a blind eye. While ZachXBT is just one actor, NounsDAO’s vote to fund him can be considered a broad attempt to normatively dissuade malicious behavior. Effectively, NounsDAO has endorsed a crypto-native “community safety officer,” cementing industry norms that make it less comfortable for scammers to set up shop.
Protocol Guild, on the other hand, encourages pro-social behavior. Protocol Guild is a public goods project which aims to fund Ethereum core infrastructure. Instead of using protocol mechanics and incentives to promote itself, operators work behind the scenes to create social alliances among crypto projects. Sponsor projects opt in to collectively shoulder the obligation to fund the core development they all rely on, promoting an ethos of generosity and mutualism.
The Nouns sponsorship of ZachXBT and Protocol Guild are among the few viable examples of the crypto industry self-regulating to limit its worst potentialities by cultivating positive-sum norms: making web3 a safe environment and supporting Ethereum core development, respectively. These norms do not derive from credible neutrality, but are opinionated civic virtues that intervene on key ecosystem-wide issues. Furthermore, Protocol Guild and NounsDAO substantiate this stance via the resources and user touch points they directly control. In both cases, the capital allocation mechanism elevates normative commitments above quantifiable financial incentives. They demonstrate that even without the law, it’s possible to build consensus around norms and foster compliance. In short, technical protocols do not provide the answer alone, but act as the basis for wider social protocols.
The Limits of “The Space”
Despite the successes of these efforts, we believe Protocol Guild and ZachXBT represent the limit of social protocols that can be built upon a social foundation of credible neutrality. This cultural desert is an inhospitable place to assemble new social normative architectures. Both endeavors are entirely voluntaristic, and the larger part of the crypto “space” does not share their sense of civic virtue.
From this vantage we can see where DAOs went wrong: because crypto discourse was never grounded in a specific social agenda, the creators of “DAO tools” got lost in meta-circular discourse about exploring their own institutional possibilities. “What is a DAO?” is a question that was never meant to be answered. Likewise, the “crypto nation” is an impossible fantasy. A nation is a legal jurisdiction and a body of people with a shared identity and culture; a crypto protocol is an institutional technology. The "space" is not a society unto itself.
The very idea of crypto being a “space” that one builds “in” is what most limits its success. This conceit runs deep in crypto, even in the desire to “onboard the next billion.” As we’ve shown, the misaligned regulatory structures native to crypto today are totally unsuited to mass adoption, and we are no longer “so early.” If crypto’s only goal was to build a non-state property system, it has already succeeded. But it is still far from producing non-state institutions that are embedded within—and promotive of—social life. Crypto needs to come to the people, not the other way around. This requires a complete change in orientation.
In contrast to tendencies of years past to put everything on-chain, what crypto needs is a significant reduction in scope, and a much richer and more active social context. To put it another way: what accounts for crypto’s three-body regulatory problem is not merely underdeveloped technical infrastructure, it is the culture of separateness itself. Crypto is a bank run on the entire cronyist financial sector. But this asset flight should be into local communities, not into an abstracted digital “space." From the rhetoric of putting real-world assets “on-chain,” to attempts of regenerative finance to transform the world solely through digital abstraction, many in the industry have characteristically missed the point.
The question is not how to add norms or social agendas to the crypto “space,” but how to join crypto with a broader institutional ecology. When we imagine a crypto that is more integrated into social life, we don’t think of an uncorrelated economy accessed through screens, but of non-extractive media of exchange and real value production that are more seamlessly integrated with our daily institutions, supportive of the interactions, organizations, and social lives we already live. These sorts of institutions simply cannot be grown if regression to the code is the only binding rule.
The frontier of free-market, permissionless protocols will always be ungovernable. But as the law encroaches on crypto’s legally gray activity, the space of viability for peer-to-peer digital institutions is rapidly diminishing. Counterintuitively, the original cypherpunk vision of credible non-state institutions may survive only through contact with cultures more full-blooded than crypto itself. If so, this next phase will certainly require protocols beyond incentives and smart contracts.
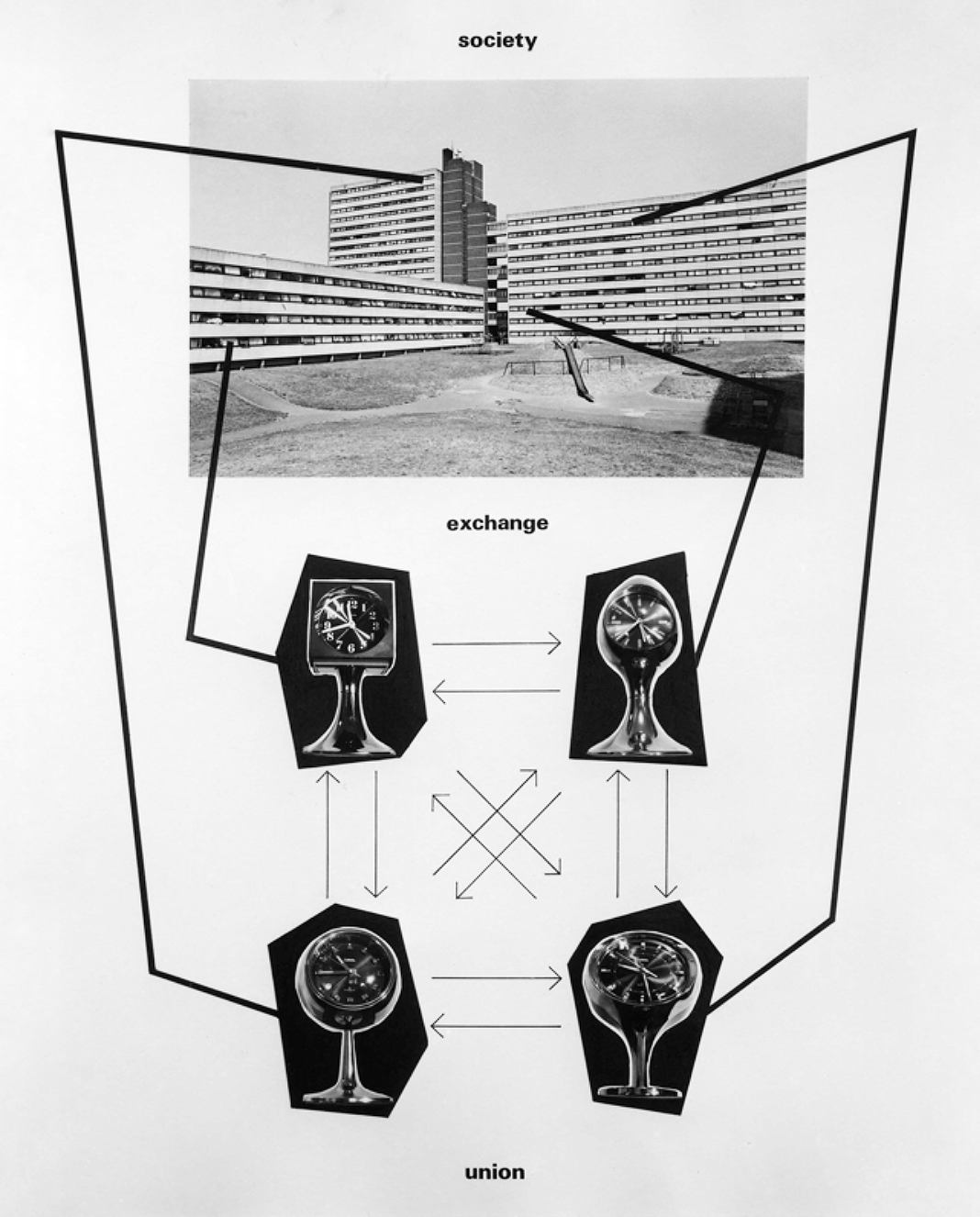 Stephen Willats, Our Interpersonal Home (1990).
Stephen Willats, Our Interpersonal Home (1990).
©2024 Other Internet Research Institute